
Understanding the Quantum Shift in Cybersecurity
Quantum cybersecurity is no longer futuristic speculation—it’s a looming reality as quantum computing rapidly advances. This article explores how to prepare your systems for the next digital threat. With its ability to calculate at exponentially faster rates than classical computers, quantum computing will unlock breakthroughs across fields such as healthcare, manufacturing, and engineering. However, the very power that fuels these innovations also presents a significant threat to current encryption standards.
As quantum computing advances, today’s encryption methods — which secure financial systems, government data, and personal privacy — become vulnerable. It’s projected that by 2040, over 20 billion digital devices will need to be updated or replaced to withstand quantum-powered cyberattacks. Furthermore, analysts estimate that global e-commerce valued at $3 trillion is already at risk if action isn’t taken to quantum-proof data security.
To stay ahead, cybersecurity leaders must adopt quantum-resistant technologies now. These include post-quantum cryptography (PQC) and quantum key distribution (QKD). Forward-thinking companies are already embracing quantum physics-based methods to modernize cryptographic systems and prepare for a post-quantum security landscape.
Why Quantum Cybersecurity Threats Can’t Be Ignored
Encryption is the bedrock of modern digital security, protecting everything from financial data and supply chains to healthcare records and national infrastructure. It enables secure communications, protects privacy, and ensures data integrity across the global digital economy. However, attackers — especially nation-state actors and well-funded cybercriminal groups — are already preparing for a quantum future.
These adversaries are using a method known as “harvest-now, decrypt-later” (HNDL), where they collect encrypted data today with the intent of decrypting it once quantum computing becomes powerful enough. This poses a significant threat to sensitive information with a long shelf life — think intellectual property, classified government documents, and medical research data that must remain protected for decades.
The implications are enormous. For example, if a quantum computer were able to crack RSA or ECC encryption, much of today’s secure internet traffic — including banking transactions, email communications, and corporate VPNs — would become instantly vulnerable. The integrity of blockchain systems, cloud platforms, and identity verification mechanisms would also be undermined.
Adding to the urgency, organizations cannot simply flip a switch and become quantum-secure overnight. Transitioning to post-quantum security involves testing and validating new cryptographic standards, upgrading legacy systems, and retraining security teams. This process can take years, especially for industries with complex or outdated infrastructure.
Moreover, sectors like defense, healthcare, finance, and energy have critical systems that are notoriously difficult to modernize. Many of these environments rely on legacy hardware with limited resources, making the adoption of quantum-safe algorithms and hardware upgrades both technically and financially challenging.
This is why it’s essential to begin preparing now — not once quantum computers are in widespread use. The cost of inaction will be far greater than the investment required to begin building a quantum-resilient infrastructure today.
Encryption is the bedrock of modern digital security, protecting everything from financial data and supply chains to healthcare records and national infrastructure. Yet, attackers — especially nation-state actors — have already begun collecting encrypted data under the assumption that it will one day be decrypted using quantum machines.
This “harvest-now, decrypt-later” strategy poses a serious risk to data with long-term sensitivity, including trade secrets, biometric data, confidential government files, and proprietary research. If your organization manages information that must remain secure for more than a decade, it’s already time to act.
Additionally, upgrading to quantum-safe systems won’t happen overnight. Organizations will face challenges with hardware limitations, budget constraints, and deployment timelines. Critical infrastructure, in particular, will require extensive testing and phased implementation.
How Quantum Security Works — and What You Can Do
Understanding the technical foundation of quantum-safe encryption starts with recognizing the limitations of today’s encryption systems. Traditional cryptographic algorithms depend on pseudo-random number generators (PRNGs) that are derived from algorithms and influenced by predictable inputs such as time, hardware states, or software behavior. Over time, even slight predictability can compromise key strength, especially when adversaries wield quantum-level computational power.
Quantum random number generators (QRNGs) offer a breakthrough solution. These devices tap into quantum mechanical processes — such as photon emission or radioactive decay — to create entropy that is truly random and not reproducible. This randomness forms the basis for highly secure cryptographic keys that are resilient even to quantum computing attacks. QRNGs are now being deployed in both hardware and cloud-based formats, offering flexibility for enterprise integration.
Incorporating QRNG technology enables organizations to strengthen critical security functions, including:
- Generation of encryption keys and secure session tokens
- Seeding of deterministic random number generators (DRBGs)
- Authentication challenges, nonces, and digital signature protocols
- Initialization vectors and cryptographic salt generation
Moreover, QRNGs play a foundational role in advancing emerging quantum cryptography methods like Quantum Key Distribution (QKD), which allows two parties to share cryptographic keys over an insecure channel with provable security guarantees.
What can your organization do today? Begin by assessing your encryption mechanisms and identifying areas that depend on strong entropy. Consider integrating commercially available QRNG solutions to boost randomness quality and start experimenting with PQC (post-quantum cryptography) libraries that are currently being vetted by NIST. By modernizing these core components now, you’ll reduce future costs and transition times as quantum cybersecurity risk becomes imminent.
At the core of quantum-safe encryption is true randomness. Current encryption systems rely on random number generators (RNGs) seeded from computer hardware and operating systems — methods that can introduce subtle patterns over time. These patterns weaken entropy, reducing the security of encryption keys.
Quantum random number generators (QRNGs), however, eliminate this risk. Devices such as advanced commercial-grade quantum random number generators (QRNGs) used in cybersecurity today use quantum processes to generate truly random sequences at speeds of up to 1 Gbit/sec. These quantum-derived keys provide the highest level of entropy, improving the security of encryption in cloud, on-premise, and hybrid environments.
In practical terms, QRNGs strengthen numerous cryptographic operations such as key generation, digital signatures, authentication protocols, and secure communication. Organizations seeking to future-proof their security architecture should prioritize these technologies alongside PQC algorithm adoption.
What Comes Next: Building a Quantum-Resilient Cyber Strategy
The urgency to build a quantum-resilient cybersecurity strategy stems from the understanding that once quantum computers reach maturity, today’s encryption standards may no longer protect our most sensitive information. Transitioning to a post-quantum landscape is not just about adopting new tools — it requires a shift in mindset, long-term planning, and strategic execution.
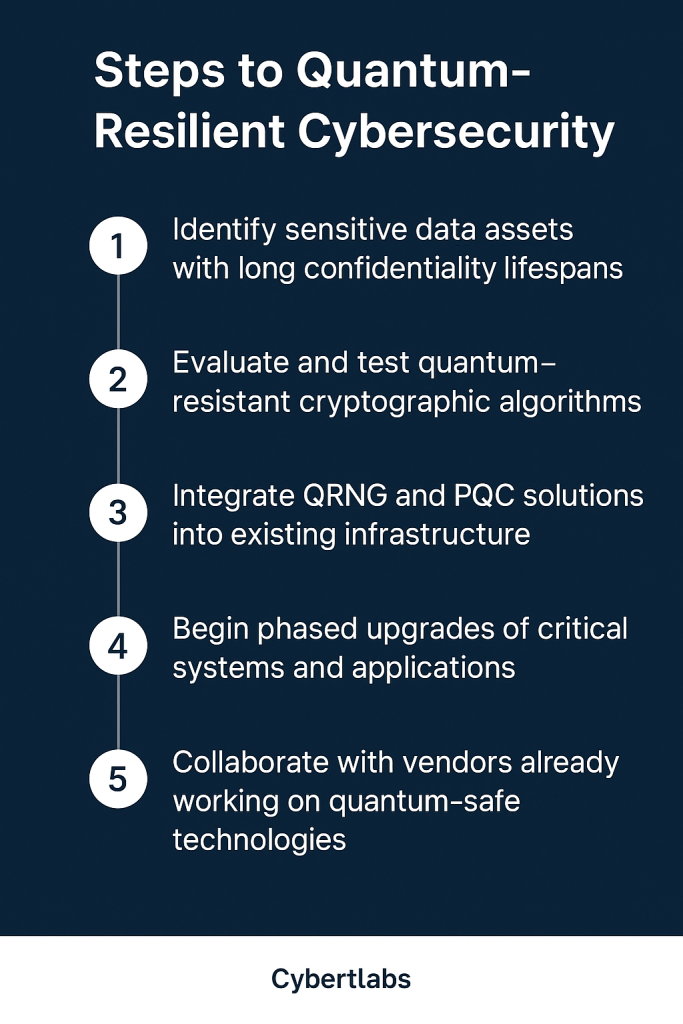
To begin, organizations must inventory their digital assets and identify data that must remain confidential for 10 years or more. This includes legal documents, health records, financial statements, intellectual property, and proprietary research. Knowing which data is at risk allows security teams to prioritize systems and applications that need quantum-safe upgrades first.
The next step is to evaluate current cryptographic dependencies and begin testing quantum-resistant algorithms — such as those being standardized by NIST. These new cryptographic techniques must be stress-tested across systems to ensure performance, interoperability, and backward compatibility with legacy infrastructure.
It’s also vital to incorporate quantum-enhanced components, such as quantum random number generators (QRNGs) or entropy-as-a-service (EaaS), into your cryptographic architecture. These technologies dramatically improve randomness in key generation, helping ensure the longevity and resilience of security controls.
Implementing a quantum strategy is not a one-time project but an evolving program. Organizations should develop a phased migration plan that includes pilot deployments, training for security teams, updates to key management practices, and close collaboration with technology vendors who are leading the development of post-quantum solutions.
Public-private collaboration will also be crucial. Enterprises should stay engaged with evolving standards and consortiums like the Quantum Economic Development Consortium (QED-C), participate in knowledge-sharing forums, and align their strategies with guidance from government and academic institutions.
By proactively preparing today, organizations can reduce future risks, avoid rushed last-minute transitions, and confidently face the quantum future with security and resilience built into the foundation of their digital infrastructure.
The risks posed by quantum computing are no longer hypothetical. With adversarial nations investing heavily in quantum R&D, the threat of quantum-enabled decryption could arrive sooner than expected. Cybersecurity teams must act preemptively, not reactively.
Building quantum resilience starts with a strategic roadmap:
Final Thoughts
Quantum cybersecurity is no longer a distant concern — it’s a strategic imperative. The convergence of powerful quantum processors and the vulnerabilities of legacy encryption demands urgent attention.
Organizations that take early action will safeguard their data, maintain trust, and avoid costly overhauls later. Start now by learning how quantum technologies work, assessing your risk profile, and partnering with providers that are already paving the way toward a secure quantum future.
Further Reading & Resources:
- QED-C: Building a Quantum-Safe Organization
- NIST: Preparing for Post-Quantum Cryptography
- WEF: Principles for Quantum Computing Governance
- CRA: Post-Quantum Readiness Challenges